Verwandte Kurse
Alle Kurse anzeigenAnfänger
Linux Basics
Learning Linux is valuable for many IT professions. For system administrators, DevOps engineers, and backend developers, it enables efficient server management, automation of software development and deployment, and the development and management of server-side applications. For network administrators, cybersecurity professionals, and data analysts, Linux knowledge helps effectively manage networks, ensure security, and analyze data.
Anfänger
Introduction to Cloud Security
Explore the foundational principles, risks, and best practices of cloud security. This course provides a comprehensive overview of how organizations protect data, applications, and infrastructure in cloud environments, using real-world case studies and conceptual frameworks.
Anfänger
Linux for DevOps Engineer
A practical, hands-on course designed for aspiring DevOps engineers to master essential Linux skills for automation, monitoring, networking, and deployment workflows in real-world environments.
The Magic Of eBPF A Revolution In Kernel Monitoring And Security
How Running Sandboxed Code In The Linux Kernel Is Changing Cloud Infrastructure

For decades, operating systems have maintained a strict, impenetrable wall between "User Space" (where your applications run) and "Kernel Space" (the privileged core that controls hardware, networking, and file systems). If an application needed to read a file or send a network packet, it had to politely ask the kernel for permission via a "System Call."
This strict separation keeps systems stable, but it creates massive bottlenecks for modern observability and security tools. If you wanted to deeply monitor network traffic or block malicious system calls, you historically had two bad options: write a slow User Space agent that constantly polls the kernel, or write a custom Kernel Module – a terrifying endeavor where a single bug causes a catastrophic kernel panic, crashing the entire server.
Enter eBPF (Extended Berkeley Packet Filter). Often described as "JavaScript for the Linux Kernel," eBPF fundamentally changes this dynamic. It allows developers to run custom, sandboxed code directly inside the OS kernel at near-native execution speed, safely and dynamically, without ever restarting the machine or modifying the kernel source code.
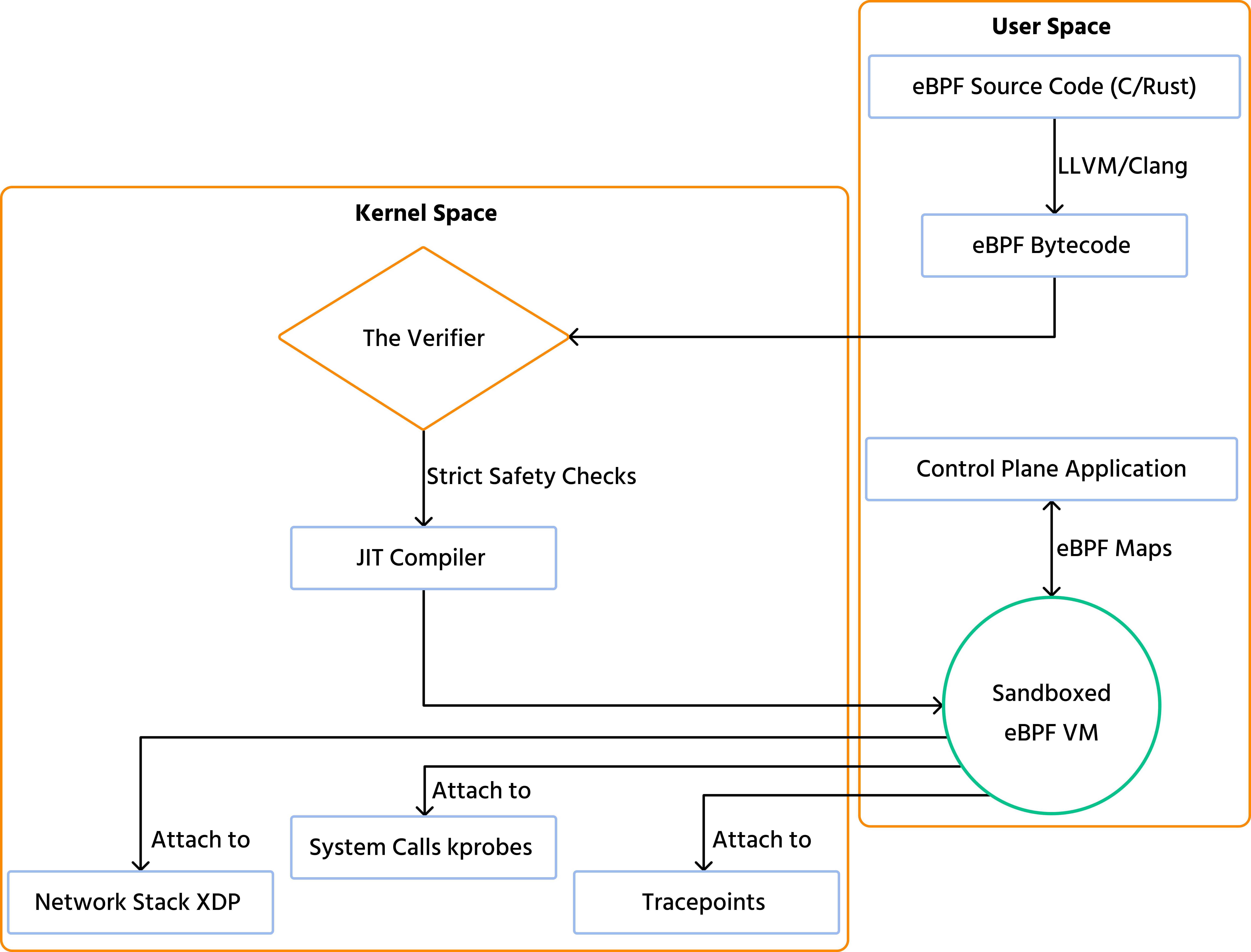
The Architecture Of eBPF The Verifier
To understand why eBPF is revolutionary, we must understand how it achieves both extreme speed and absolute safety. You cannot simply inject random code into the kernel.
When a developer writes an eBPF program (usually in C or Rust), it is compiled into a specific eBPF bytecode. Before this bytecode is allowed to run in the kernel, it must pass through the most critical component of the architecture: The Verifier.
The Verifier acts as an ultra-strict bouncer. It analyzes the bytecode mathematically before execution to guarantee that the program is completely safe. It ensures that the program will not crash the kernel, will not access unauthorized memory, and will always terminate (no infinite loops allowed). Once the Verifier approves the program, a Just-In-Time (JIT) compiler translates the bytecode into native machine instructions for maximum performance.
Run Code from Your Browser - No Installation Required

Supercharging Observability And Security
Because eBPF programs run directly inside the kernel, they have a god-like view of the entire system. They can be attached to virtually any event happening in the OS, such as a network packet arriving, a file being opened, or a specific function executing.
1. Zero Instrumentation Observability
In the past, to monitor an application (like a Node.js or Java service), developers had to modify their code to include specific instrumentation libraries. With eBPF, this is no longer necessary. An eBPF program can attach to kernel tracepoints and monitor HTTP requests, database queries, and latency directly from the OS level, without writing a single line of telemetry code in the application itself.
2. Lightning Fast Networking
Modern Kubernetes environments rely heavily on eBPF-based networking (most notably the open-source project Cilium). By using a feature called XDP (eXpress Data Path), eBPF can intercept and route network packets at the network driver level, before they even reach the standard Linux networking stack. This allows for load balancing and DDoS protection at hardware-like speeds.
3. Proactive Security
Traditional security tools look at logs after an event has occurred. eBPF enables real-time, proactive security. If a compromised container attempts to execute a malicious binary or access a forbidden directory, an eBPF program attached to the execve system call can evaluate the action and instantly terminate the process before the kernel even executes the command.
| Feature | User Space Agents | Traditional Kernel Modules | eBPF Programs |
|---|---|---|---|
| Safety | High (Cannot crash the OS) | Very Low (Bugs cause Kernel Panics) | High (Guaranteed safe by the Verifier) |
| Performance | Low (High context-switching overhead) | Very High (Native speed) | Very High (JIT compiled) |
| Update Agility | Fast (Deploy like normal apps) | Slow (Requires kernel recompilation/reboot) | Fast (Load and unload dynamically) |
| System Visibility | Limited (Requires APIs/Logs) | Complete | Complete |
Conclusion
The introduction of eBPF is one of the most significant paradigm shifts in systems engineering in the last decade. By safely unlocking the power of the Linux kernel, eBPF has rendered traditional approaches to networking, security, and observability obsolete. As cloud-native architectures grow more complex, the ability to program the operating system dynamically without sacrificing stability is not just an optimization – it is a mandatory requirement for modern enterprise infrastructure.
Start Learning Coding today and boost your Career Potential

FAQs
Q: What languages can I use to write eBPF programs?
A: The core eBPF programs that run in the kernel are primarily written in restricted C or Rust, which compile down to eBPF bytecode. However, the User Space applications that manage and interact with these programs can be written in almost any language, including Go, Python, and C++, using libraries like bcc or cilium/ebpf.
Q: Does eBPF add performance overhead to my system?
A: The overhead is extremely minimal, typically less than 1-2%. Because eBPF programs are JIT-compiled into highly optimized native machine code and run without crossing the costly User Space/Kernel Space boundary, they are orders of magnitude faster than traditional monitoring agents.
Q: Is eBPF only available on Linux?
A: Originally, yes. However, recognizing its massive potential, the industry (led by Microsoft) has created the "eBPF for Windows" project, which is actively porting the eBPF architecture and toolchains to run natively within the Windows operating system kernel as well.
Verwandte Kurse
Alle Kurse anzeigenAnfänger
Linux Basics
Learning Linux is valuable for many IT professions. For system administrators, DevOps engineers, and backend developers, it enables efficient server management, automation of software development and deployment, and the development and management of server-side applications. For network administrators, cybersecurity professionals, and data analysts, Linux knowledge helps effectively manage networks, ensure security, and analyze data.
Anfänger
Introduction to Cloud Security
Explore the foundational principles, risks, and best practices of cloud security. This course provides a comprehensive overview of how organizations protect data, applications, and infrastructure in cloud environments, using real-world case studies and conceptual frameworks.
Anfänger
Linux for DevOps Engineer
A practical, hands-on course designed for aspiring DevOps engineers to master essential Linux skills for automation, monitoring, networking, and deployment workflows in real-world environments.
Inhalt dieses Artikels